Google Messages Crashing/Hanging Fix
In this blog post, I will show how I fixed the Google Messages app from freezing. Please keep in mind, this fix worked for me and a couple of other people. While it may not work for everyone, I am sharing it in the hopes that it might help someone else experiencing the same problem.
Background: For the last 3 months, I have been encountering an issue with Google Messages. Every time I opened the app, it would completely freeze within 10 seconds, forcing me to close it manually. Initially it seemed to go away with a Google Messages update. Unfortunately, it started freezing on me again.
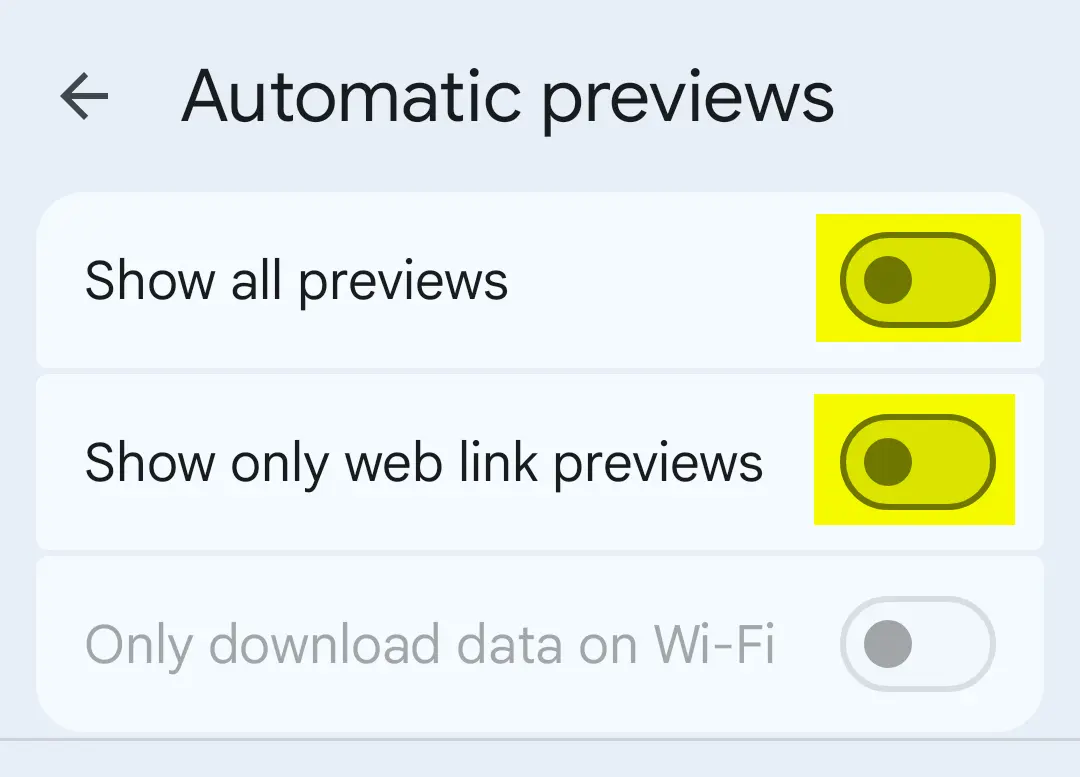
After tinkering with it for a bit, I figured out the “Automatic previews” feature was causing the app to hang. Disabling the “Automatic previews” option resolved the issue.
If you wish to try the fix for yourself, here is what to do.
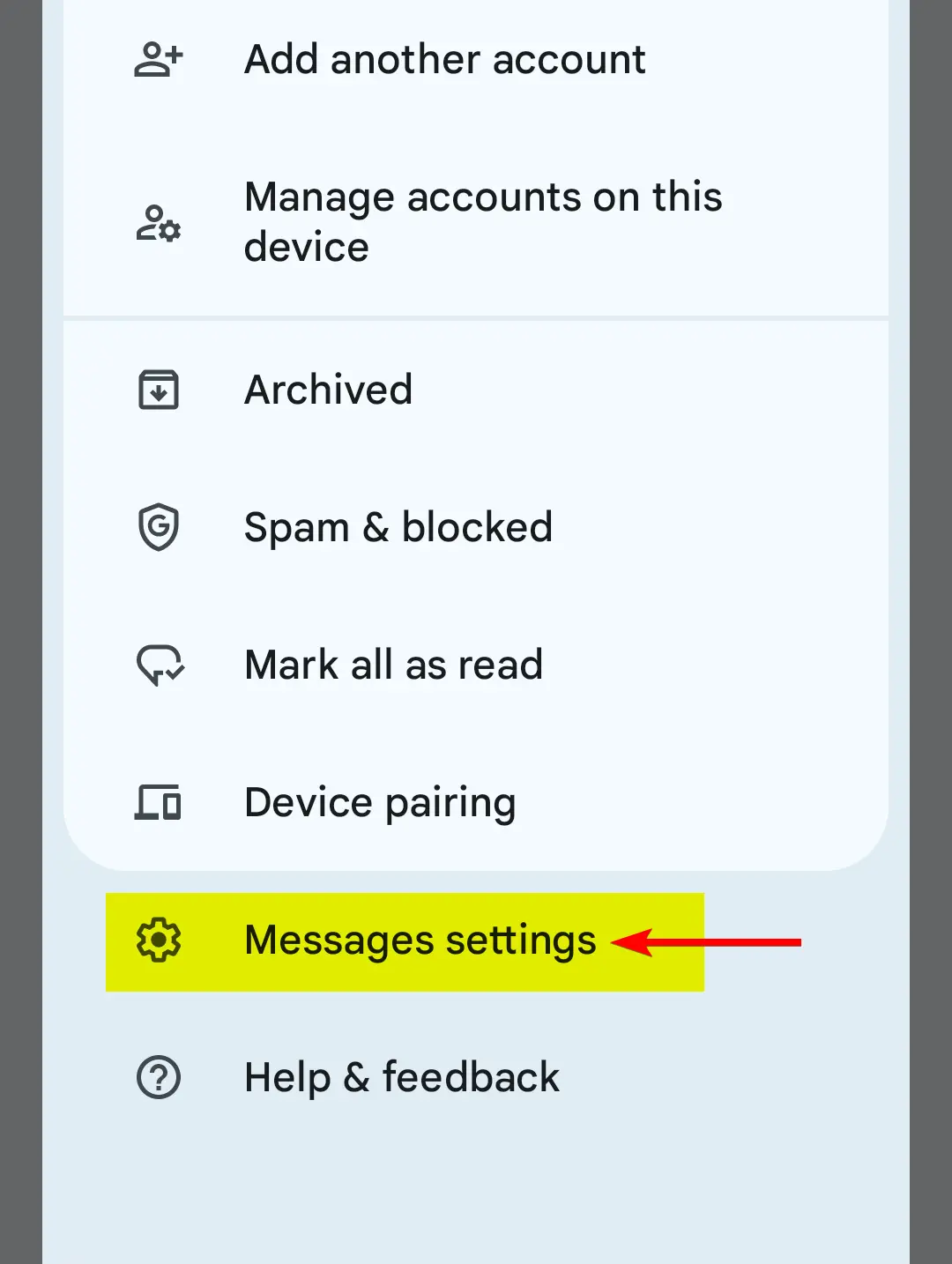
1. On the top-right of the app, tap on the icon as shown in the image below.
2. Open the settings menu.
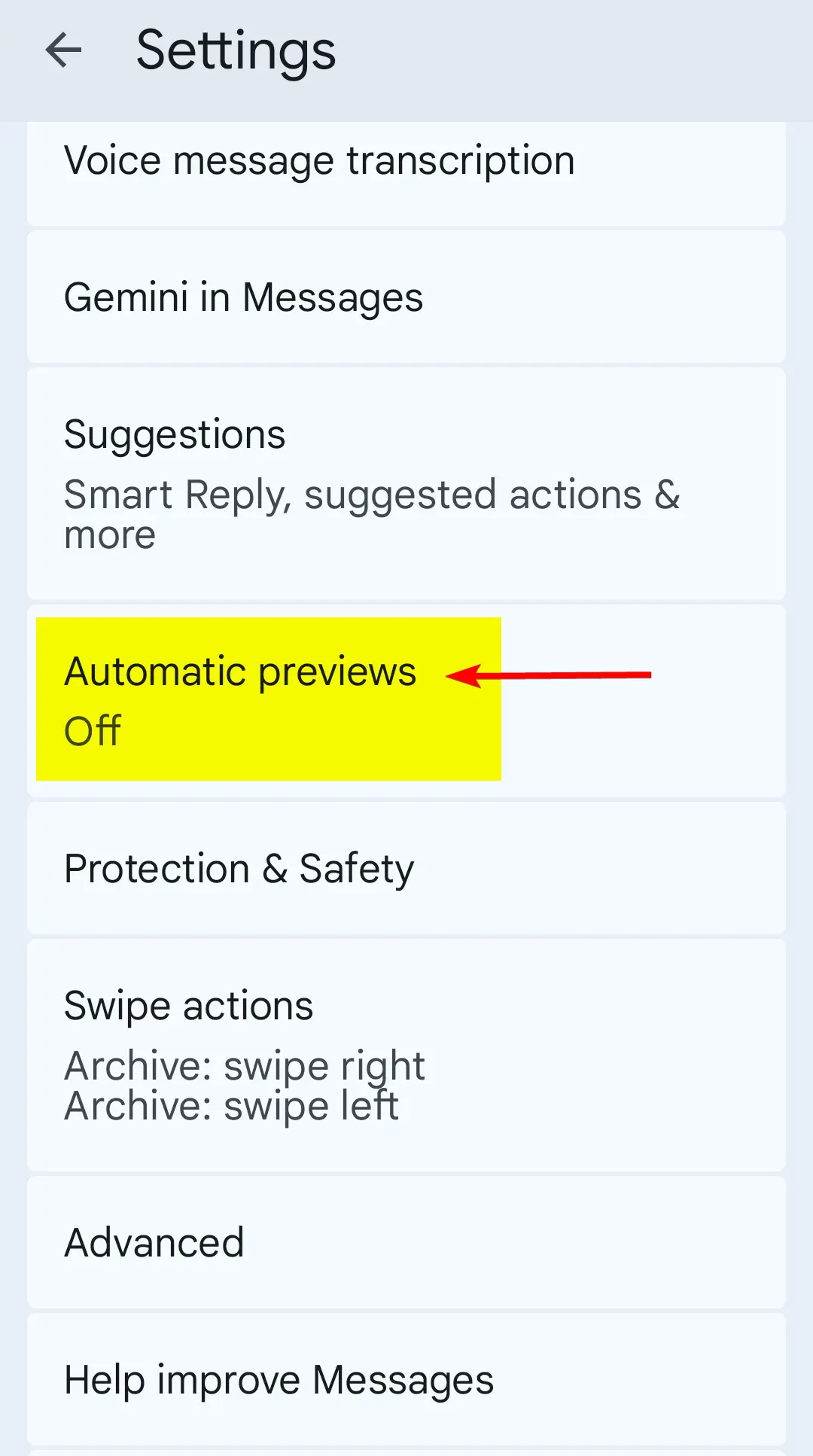
3. Find “Automatic previews”, and tap on that.
4. Make sure the highlighted options are disabled.
And that is it. This worked for me, and hopefully this will work for you too.
Posted in Android, Mobile Phone, Software, Tips & Tutorials
Are Web Browser Extensions Safe to Use? (2025 Update)
Several years ago, I wrote about the potential risks associated with web browser extensions (also referred to as “add-ons”) being able to abuse their power and access sensitive user data.
I said if someone has installed a malicious browser extension, their web browsing data (e.g., browsing history, password credentials, what they type into a website, etc.) may get sent directly to the extension’s creator, putting the user’s online security and privacy at risk.
Today, I received an email with a link to a news article, explaining how 18 separate web extensions for Edge and Google Chrome were caught spying on people.
Here is the link to the article: https://www.malwarebytes.com/blog/news/2025/07/millions-of-people-spied-on-by-malicious-browser-extensions-in-chrome-and-edge
[Click here to view article as a PDF.]
This just goes to show, always be mindful about which web browser extensions you choose to install.
Update 08-22-2025
Here’s another example of why you should be careful with web browser extensions.
Chrome VPN Extension With 100k Installs Screenshots All Sites Users Visit
Posted in Android, Computers, General, Internet and Servers, Mobile Phone, Security, Software
Are Web Browser Extensions Safe to Use?
Many people use web browser add-ons (such as Ad-blockers) for their everyday browsing. What most people are unaware of is that many of these add-ons have permissions that allow the add-on to view the content of the web pages the user is viewing.
The problem? If someone has installed a malicious add-on, their web browsing data (e.g., browsing history, password credentials, what they type into a website, etc.) would have been sent to the add-on’s creator. Now I am not implying that every single web browser add-on does this, but there is a very high potential that this can happen.
Would only using open-source browser add-ons be a safe option? Well open-source add-ons would definitely lower the chance that someone would get away with spying on you. However open-source projects do not have a spotless security track record either. There is still some risk.
Even Mozilla themselves warn about this problem with web browser add-ons (also called extensions).
Here is an example of what I am talking about (https://www.zdnet.com/article/mozilla-removes-avast-and-avg-extensions-from-add-on-portal-over-snooping-claims/).
Posted in Android, Computers, General, Internet and Servers, Mobile Phone, Security, Software