Google Messages Crashing/Hanging Fix
In this blog post, I will show how I fixed the Google Messages app from freezing. Please keep in mind, this fix worked for me and a couple of other people. While it may not work for everyone, I am sharing it in the hopes that it might help someone else experiencing the same problem.
Background: For the last 3 months, I have been encountering an issue with Google Messages. Every time I opened the app, it would completely freeze within 10 seconds, forcing me to close it manually. Initially it seemed to go away with a Google Messages update. Unfortunately, it started freezing on me again.
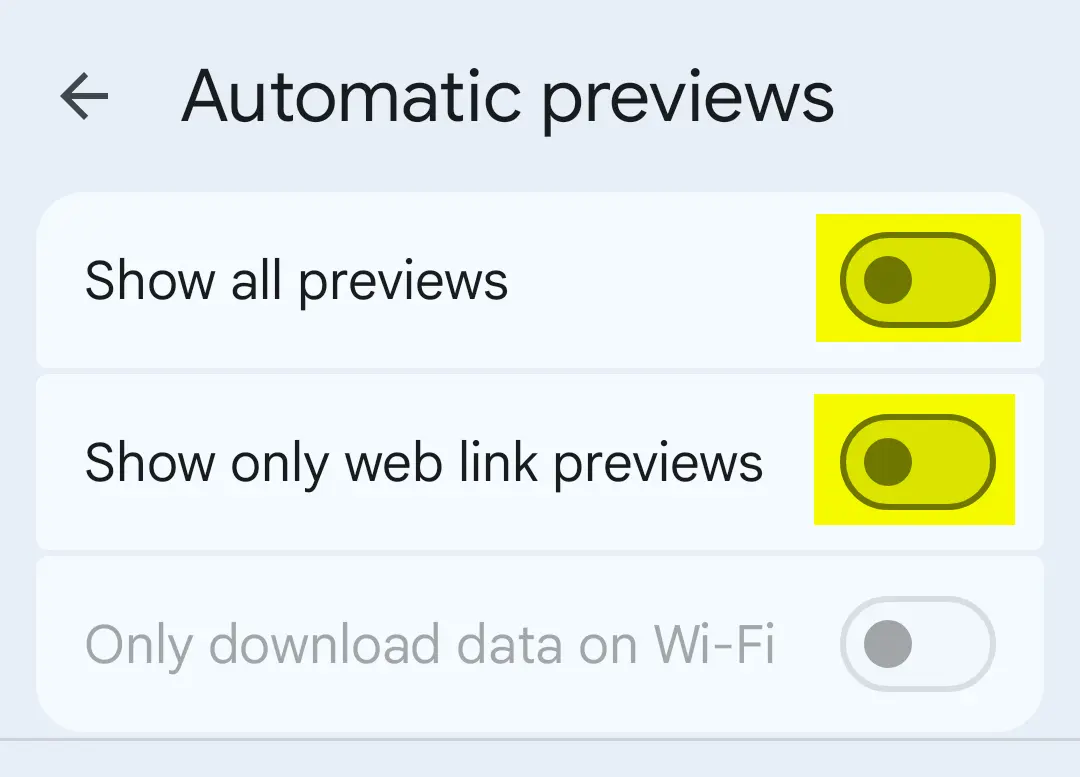
After tinkering with it for a bit, I figured out the “Automatic previews” feature was causing the app to hang. Disabling the “Automatic previews” option resolved the issue.
If you wish to try the fix for yourself, here is what to do.
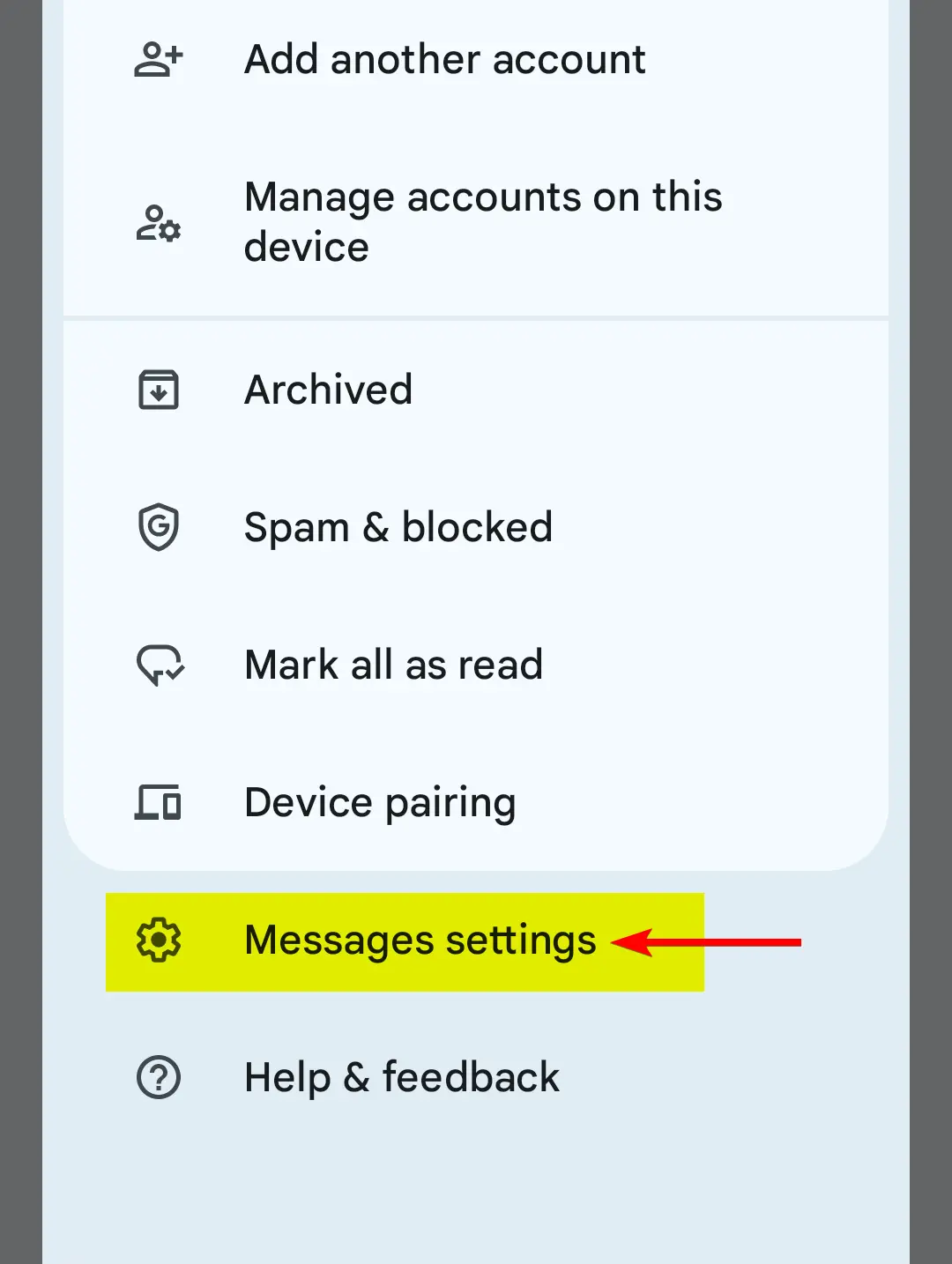
1. On the top-right of the app, tap on the icon as shown in the image below.
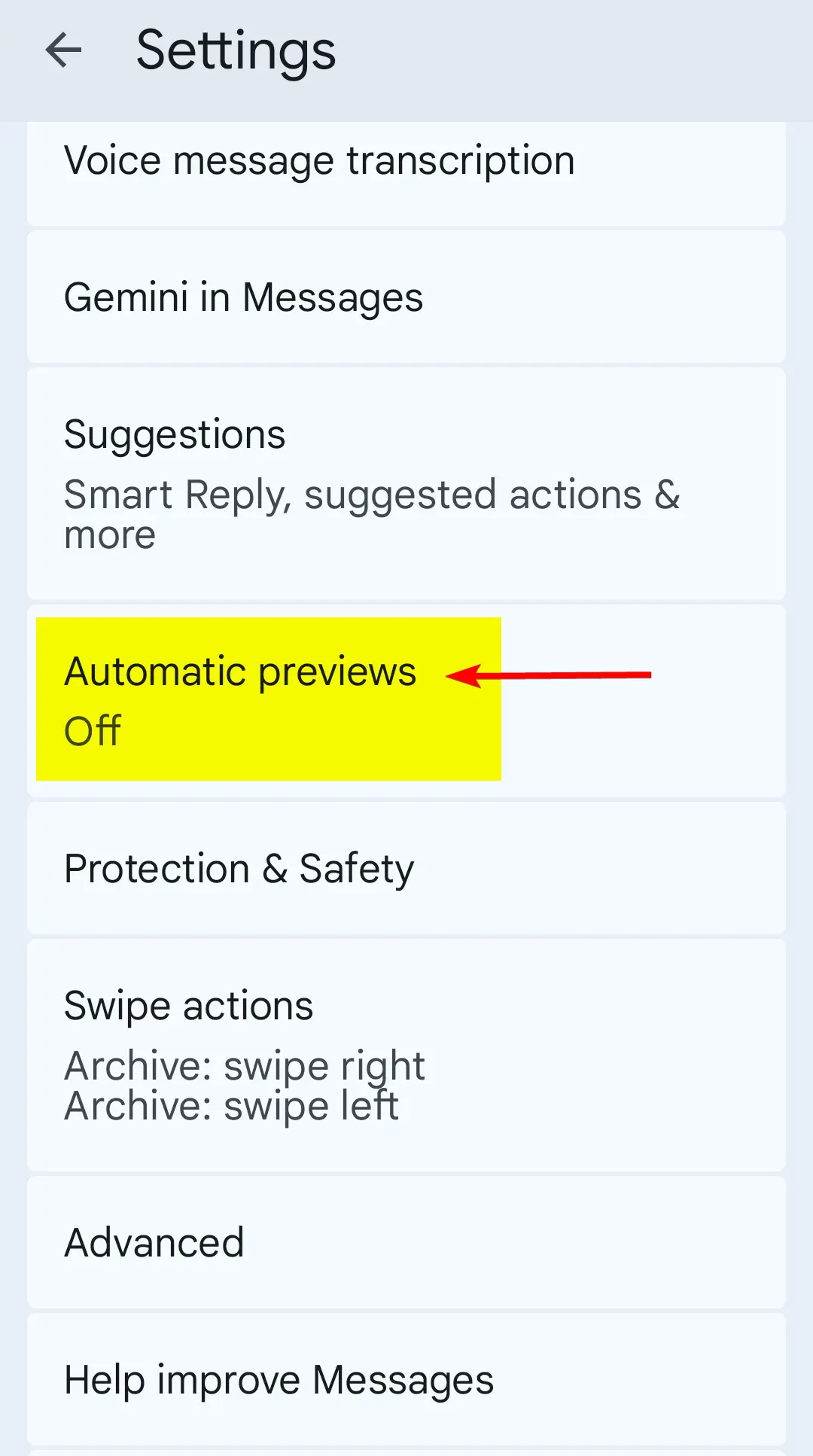
2. Open the settings menu.
3. Find “Automatic previews”, and tap on that.
4. Make sure the highlighted options are disabled.
And that is it. This worked for me, and hopefully this will work for you too.
Posted in Android, Mobile Phone, Software, Tips & Tutorials
Are Web Browser Extensions Safe to Use? (2025 Update)
Several years ago, I wrote about the potential risks associated with web browser extensions (also referred to as “add-ons”) being able to abuse their power and access sensitive user data.
I said if someone has installed a malicious browser extension, their web browsing data (e.g., browsing history, password credentials, what they type into a website, etc.) may get sent directly to the extension’s creator, putting the user’s online security and privacy at risk.
Today, I received an email with a link to a news article, explaining how 18 separate web extensions for Edge and Google Chrome were caught spying on people.
Here is the link to the article: https://www.malwarebytes.com/blog/news/2025/07/millions-of-people-spied-on-by-malicious-browser-extensions-in-chrome-and-edge
[Click here to view article as a PDF.]
This just goes to show, always be mindful about which web browser extensions you choose to install.
Update 08-22-2025
Here’s another example of why you should be careful with web browser extensions.
Chrome VPN Extension With 100k Installs Screenshots All Sites Users Visit
Posted in Android, Computers, General, Internet and Servers, Mobile Phone, Security, Software
RPCS3 Settings Guide for Uncharted: Drake’s Fortune
This tutorial will show you which custom settings to use with Uncharted: Drake’s Fortune on the RPCS3 (PlayStation 3) emulator. These settings are what I personally use. As always, your results may vary.
Known Problems that I Experienced
- FPS drop when shaders get compiled (nothing you can really do about that)
- FPS drop when a lot of activity is on the screen (e.g., several enemies on the screen at once)
- Texture pop-in
- Texture flicker
Prerequisites
- Latest copy of RPCS3 (Download Page)
- A copy of Uncharted: Drake’s Fortune for use with the emulator.
- A fairly beefy computer (for best performance; can work on slower computers).
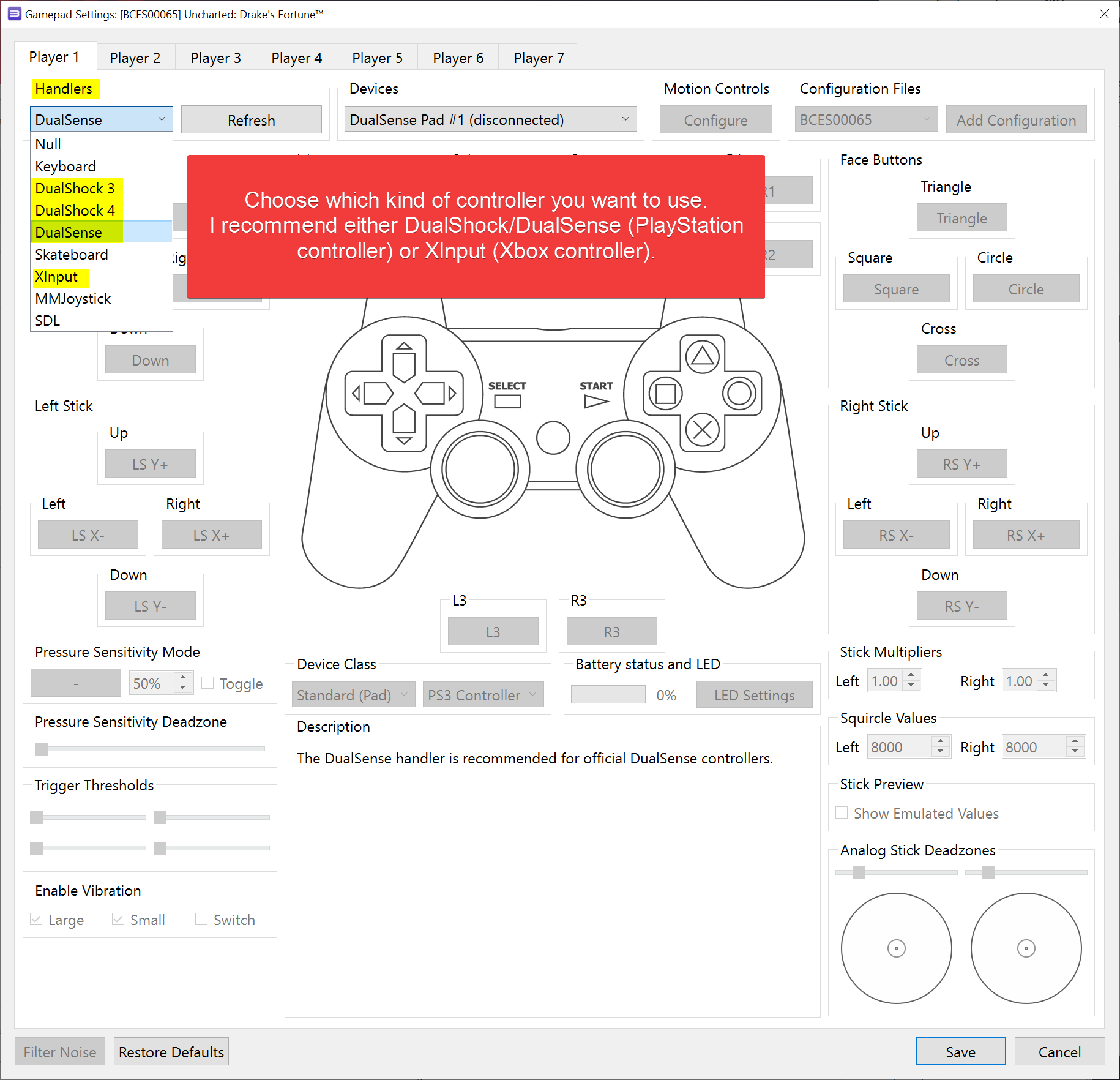
- A PlayStation controller (preferred) or an Xbox controller (connected via wired or wireless).
- First off, add the game to RPCS3 to get started.
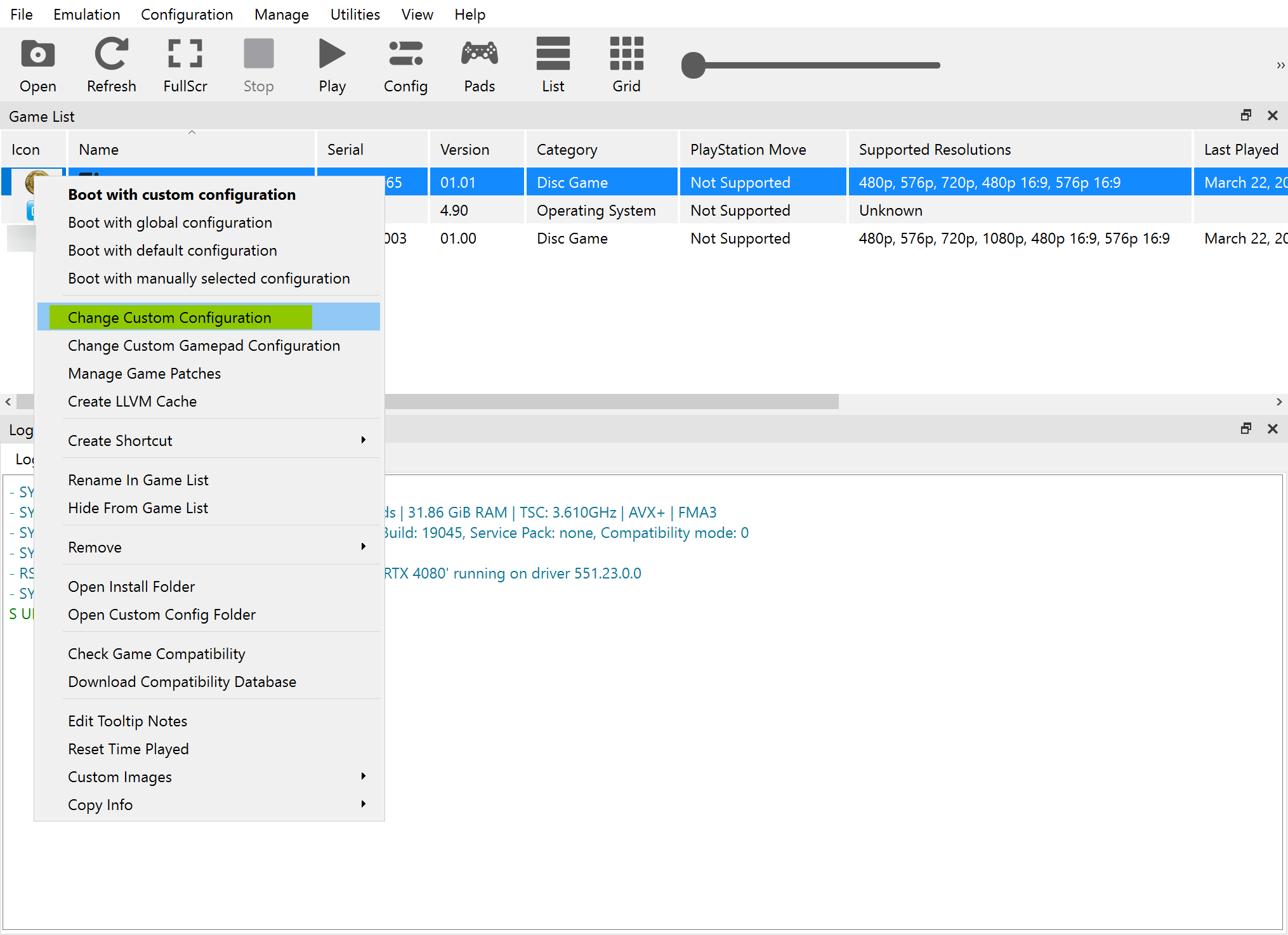
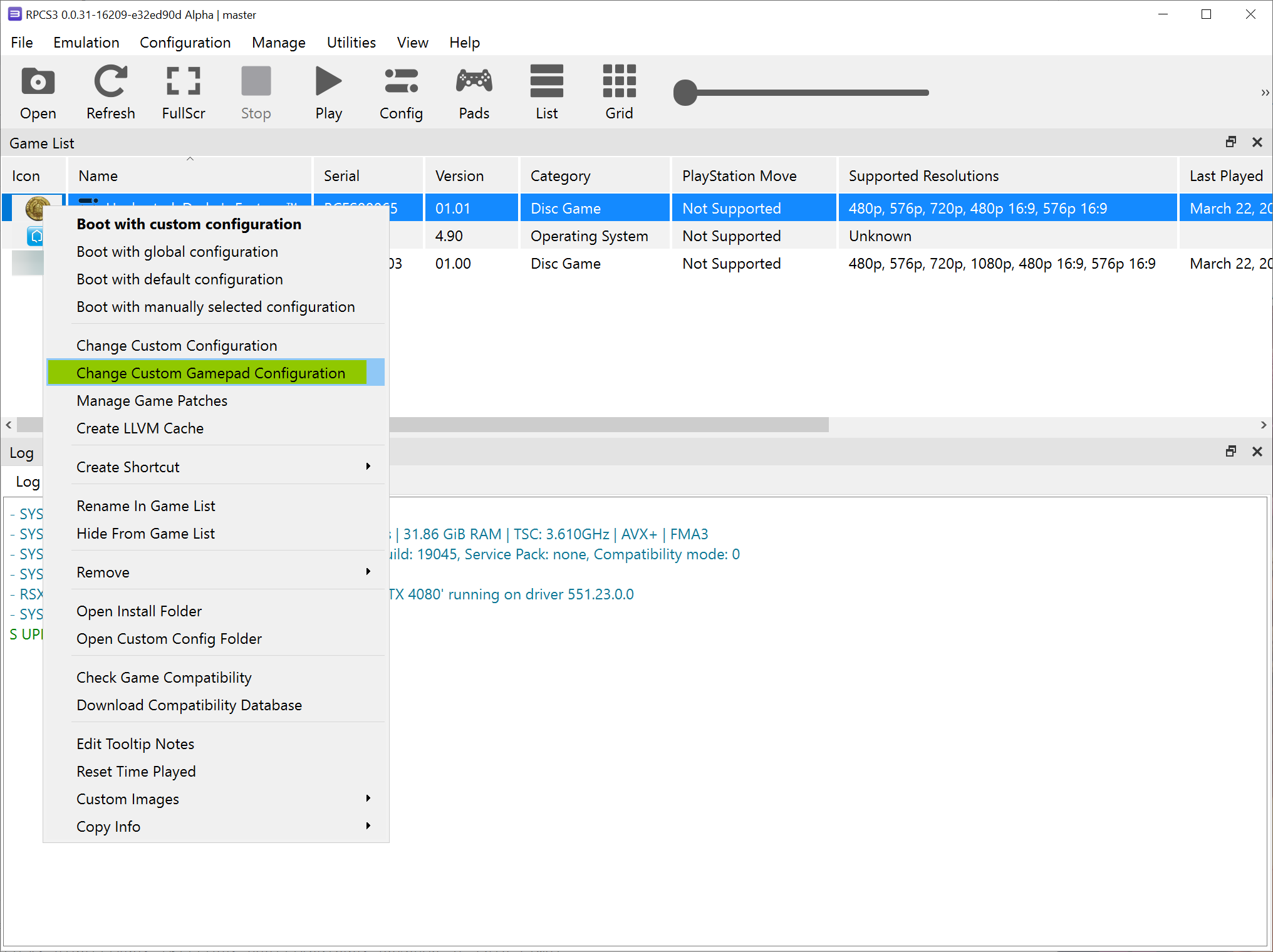
- Now right-click on the game and select “Change Custom Configuration”.
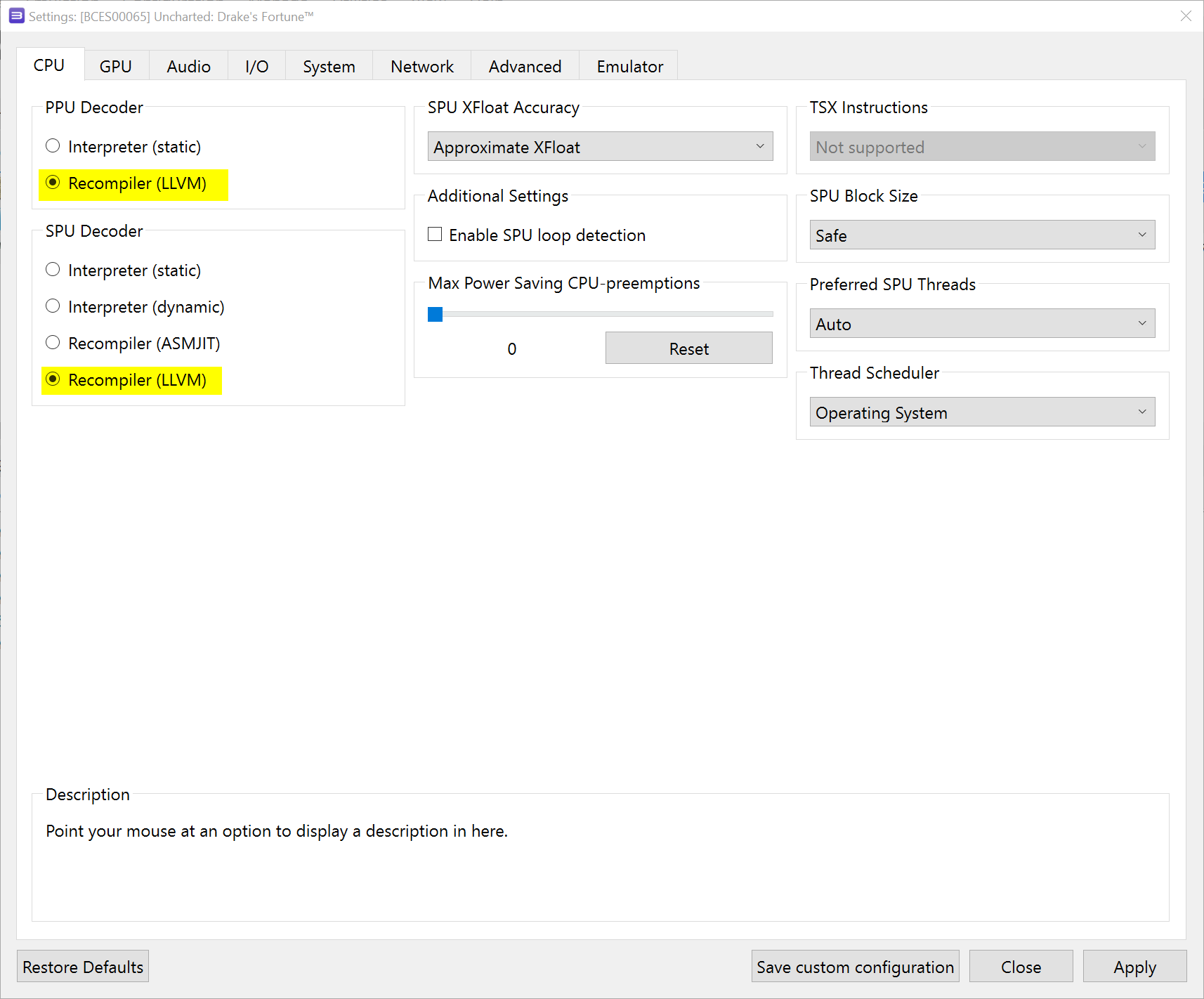
- Now we are at the configuration for the emulator’s CPU. Make sure your settings match what is shown in the screenshot.
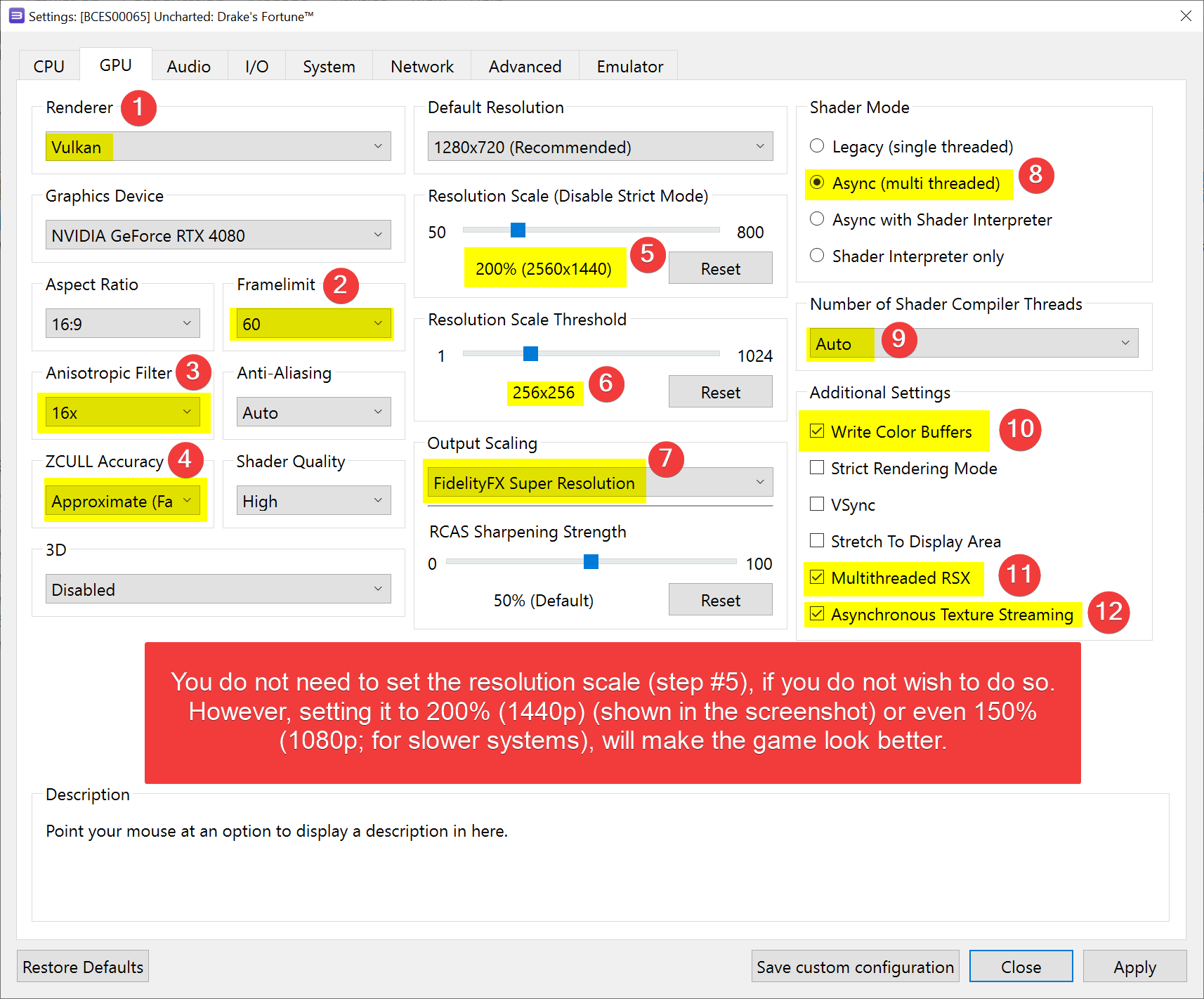
- Now click on the “GPU” tab and set your settings to what is shown in the following screenshot.
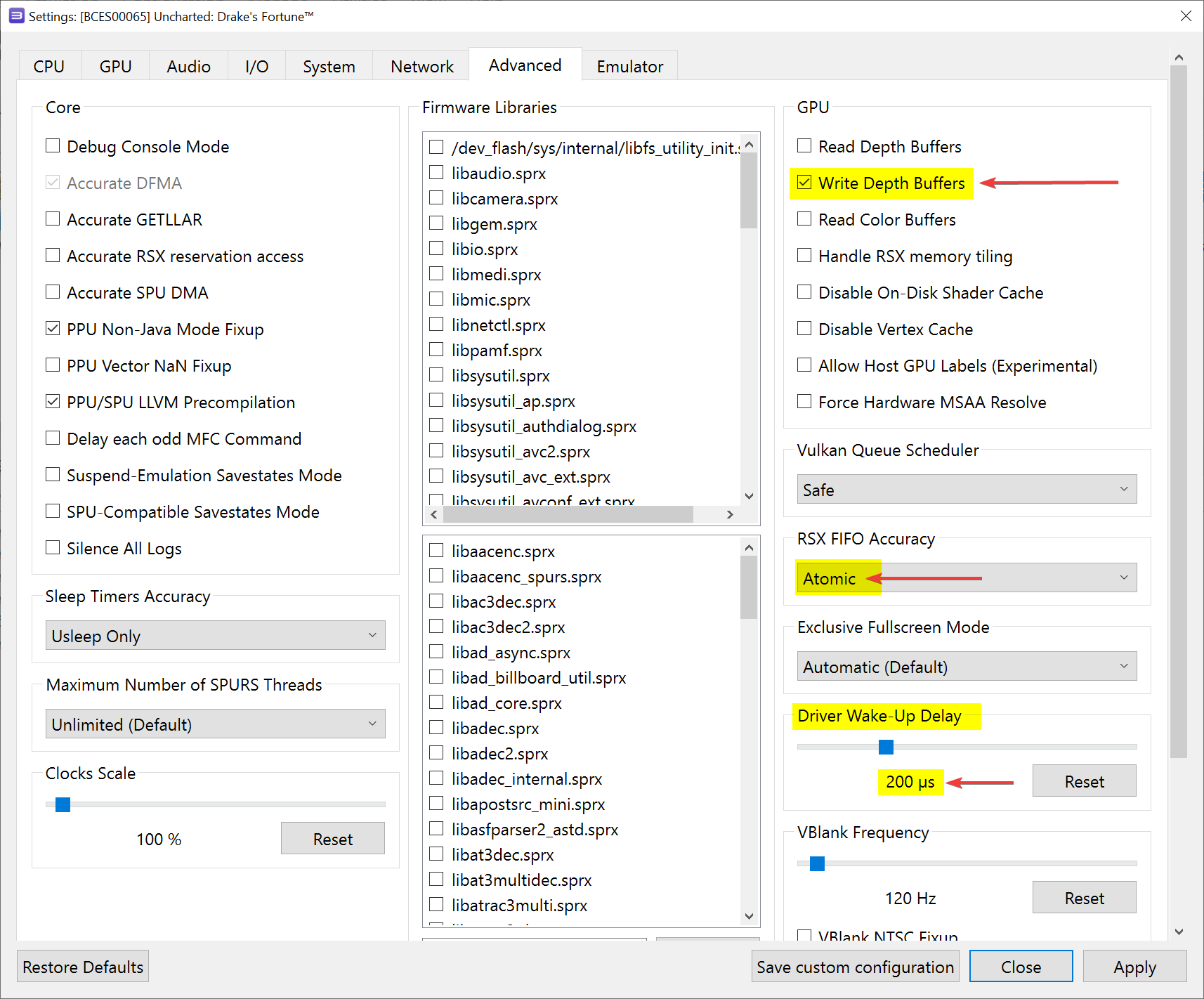
- Click on the “Advanced” tab and set your settings to what is shown in the following screenshot.
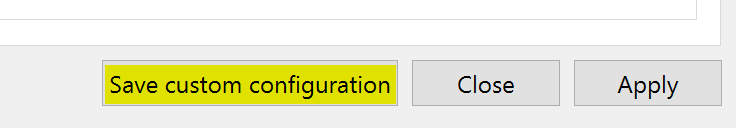
- Now click on the “Save custom configuration” button at the bottom of the configuration box.
- Right-click on the game again and this time select “Change Custom Gamepad Configuration”.
- Now set your controller input type.
- Click the “Save” button.
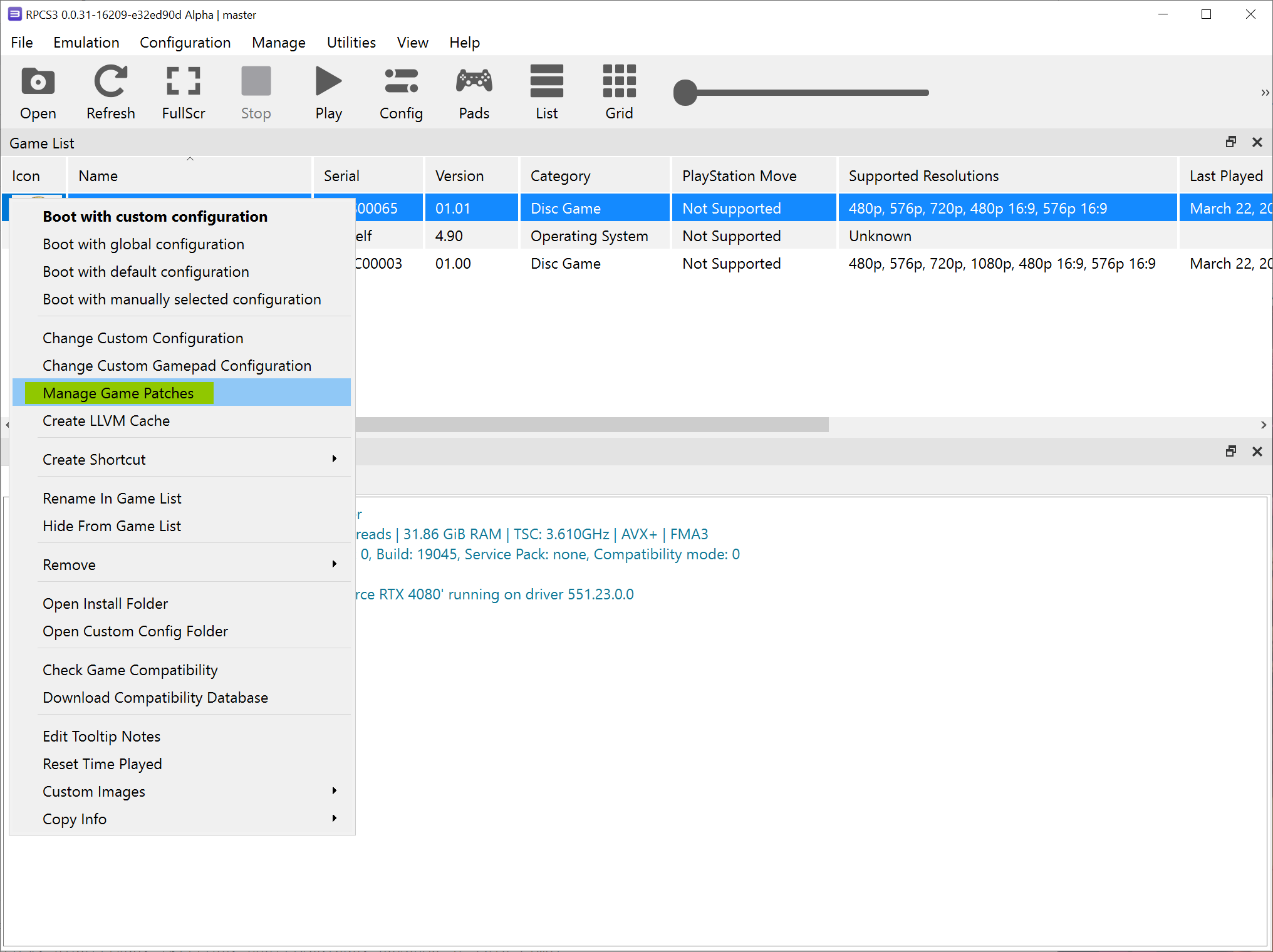
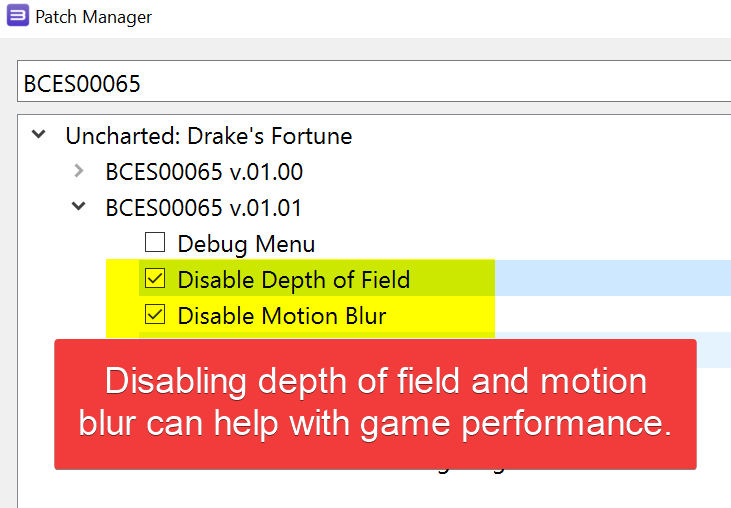
- Again, right-click on the game and select “Manage Game Patches”.
- Select the game patches as shown in the screenshot. Your version of the game may show different patches in the list. However, the two patches you want to select should still be available.
That’s it! You will want to run the game to see if everything is in working order.
Posted in Computers, Software, Tips & Tutorials, Video Games