Some of my readers, especially longtime ones, may remember that I have warned multiple times about being careful which extensions you choose to install in your web browser. Installing the wrong one, especially one that contains malicious code, can compromise your computer’s security.
This time, it is a lesson on being careful which extension you install in Visual Studio Code (a.k.a. VS Code). In a nutshell, an employee at GitHub installed (or at least updated) an extension that had been contaminated with malware code. The extension then proceeded to steal the employee’s credentials and gain access to tons of GitHub’s own private repositories.
The report claimed the malware stole:
- AWS keys
- Database passwords
- Kubernetes tokens
- SSH credentials
I would venture a guess that other IP (intellectual property) was stolen too.
I will let you read the full report from X below.
Posted in Cloud, Computers, General, Internet and Servers, Operating Systems, Security, Software
In this short tutorial, I will show you how to enable and disable the Snap Windows feature in Windows 11.
Snap Windows are useful when you want to quickly arrange multiple windows on your desktop. However, they can become irritating and even a hindrance to some people, if you want to position a window on the edge of the screen without triggering auto-snap.
With that little introduction out of the way, let us begin.
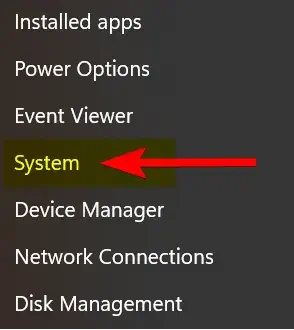
- Right-click on the Windows Start icon
 and click on the “System” menu option.
and click on the “System” menu option.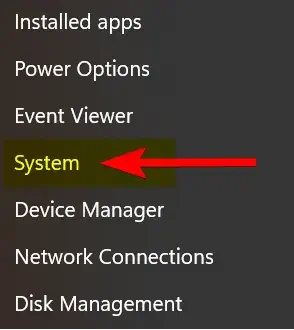
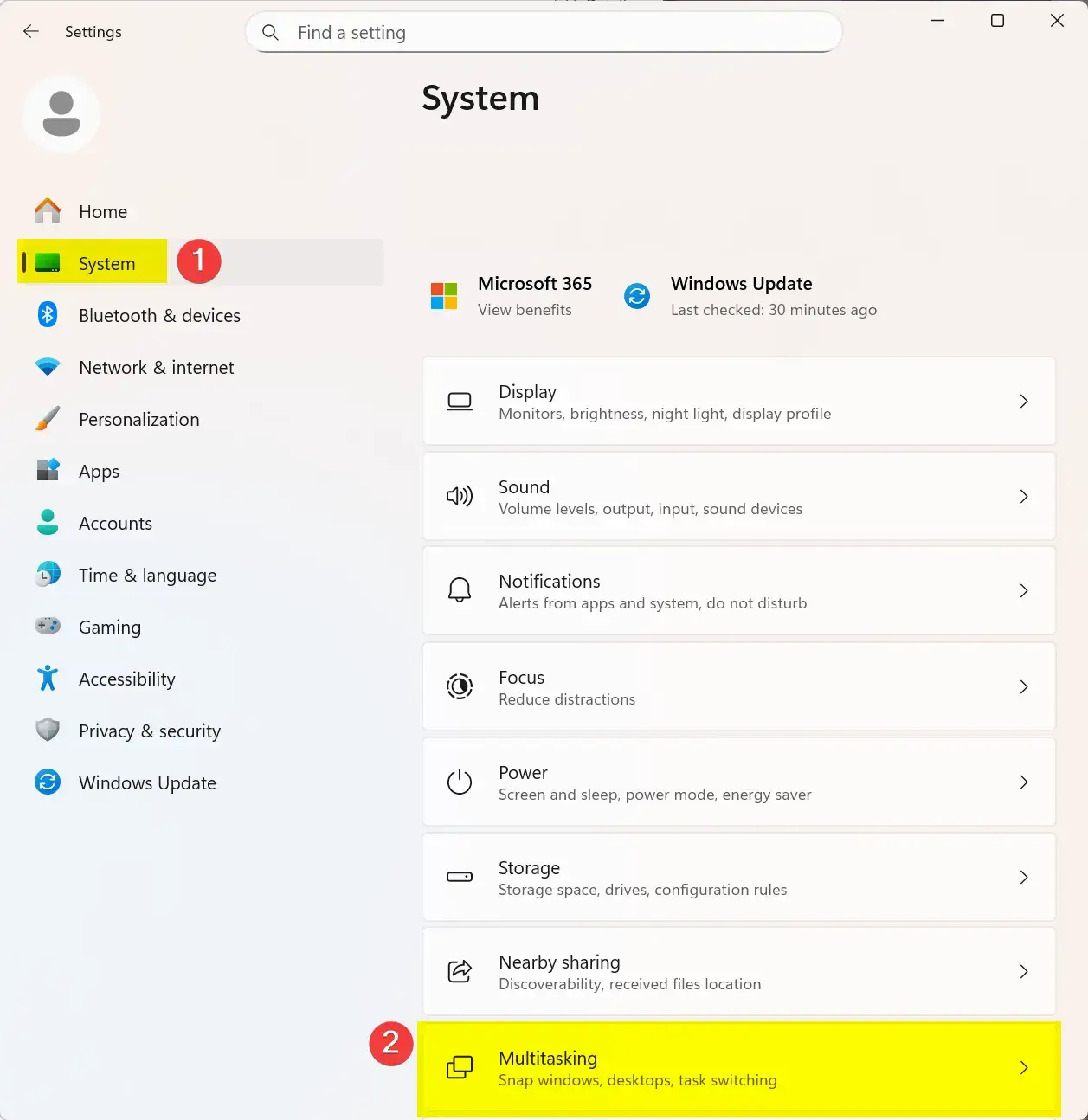
2. On the left-side panel, click on “System”, then click on the “Multitasking” option.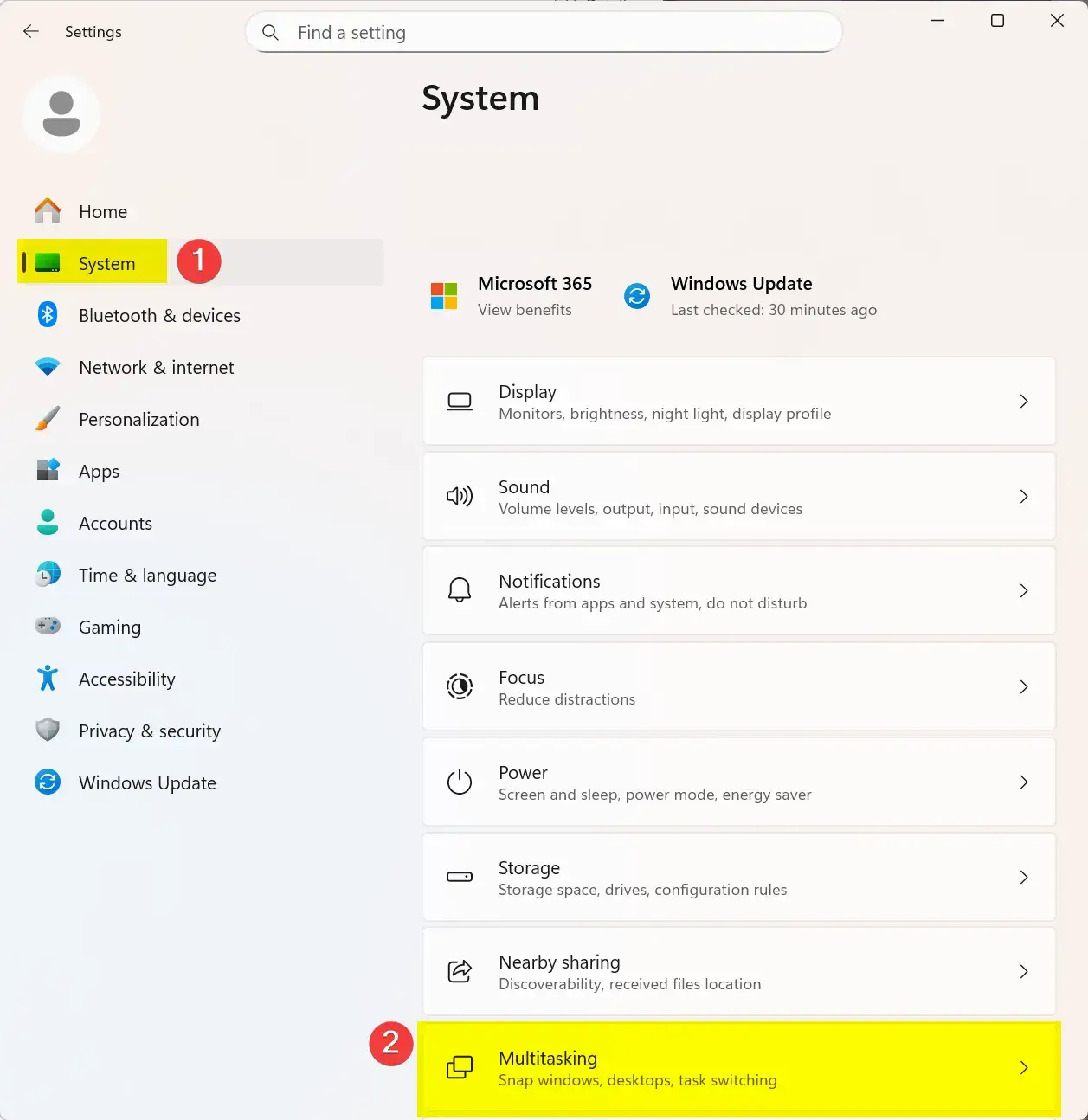
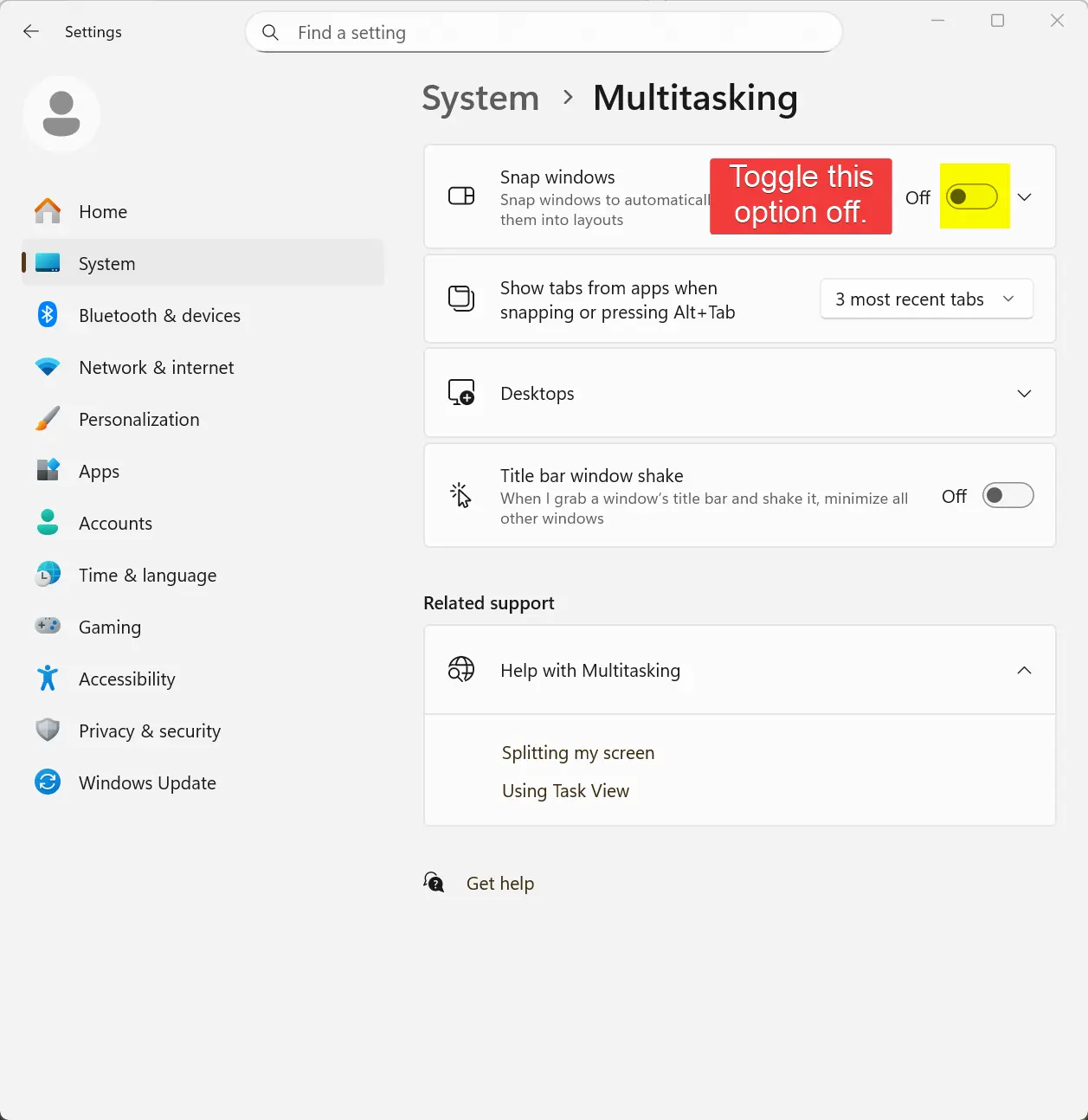
3. Now locate the “Snap windows” option, and click the toggle button to disable it. Of course, if sometime later on you wish to re-enable this feature, just click on the toggle button again to re-enable it.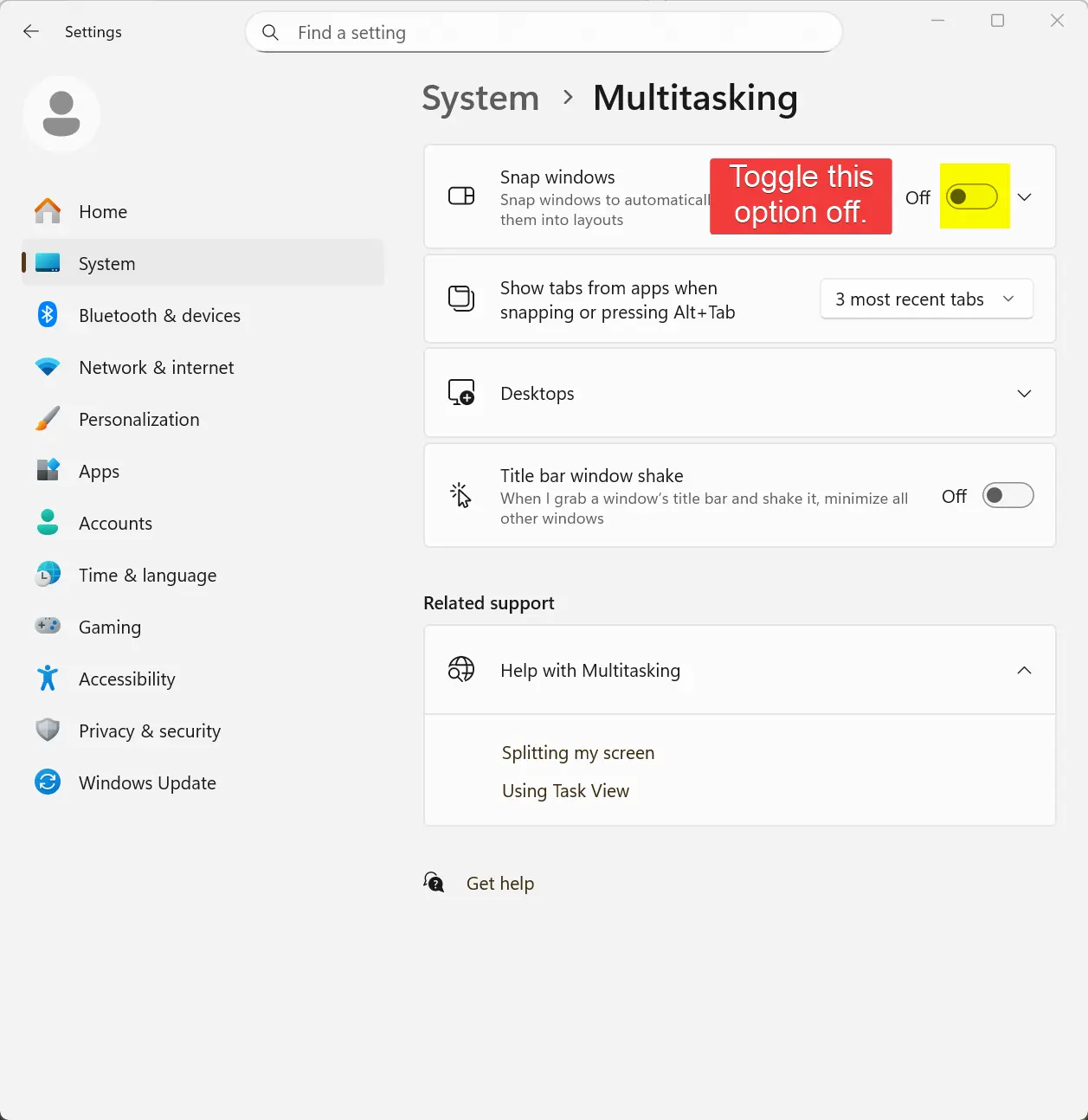
That is the end of this tutorial. I hope someone finds it useful.
Posted in Computers, Operating Systems, Tips & Tutorials
In this blog post, I will explain how to show file extensions, and how to view hidden files and folders on your Windows 11 system.
By default, Windows 11 hides file extensions, and any files and folders marked with the attribute “hidden”. At some point, you may have a need to change a file’s extension manually (e.g., “.txt” to “.ini“). It can also be useful to see any hidden files and folders on your computer.
ℹ️ Notice
No reboot is required for these changes to take effect.
- Open the File Explorer.
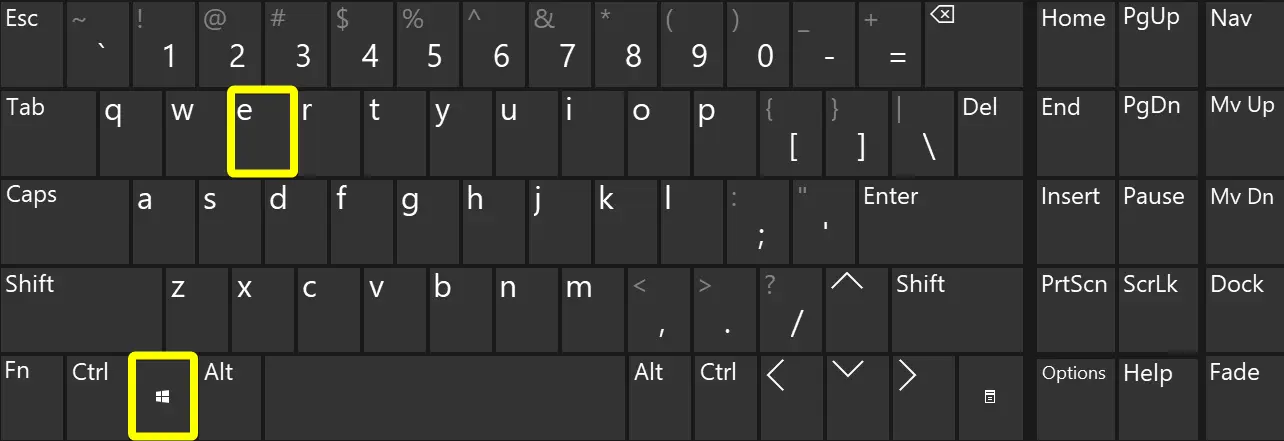
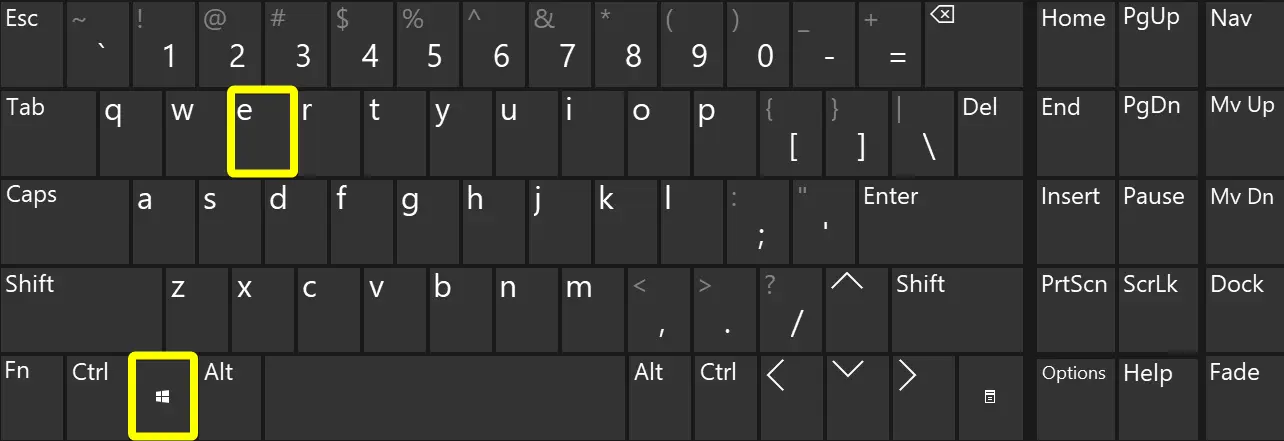
- If you wish, you can use the [ Windows Key + E ] keyboard combination to open File Explorer.
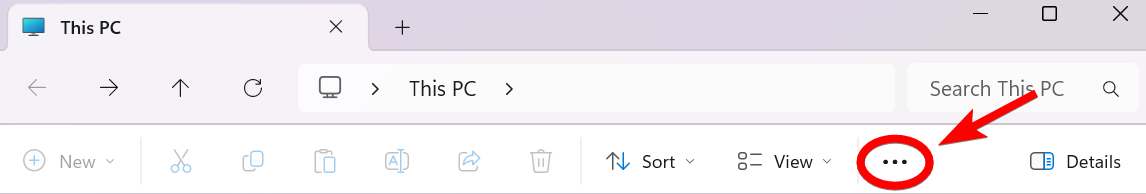
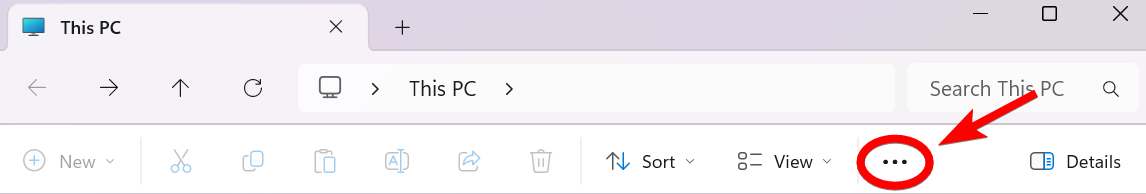
- After the File Explorer opens, click on the ellipsis menu button.
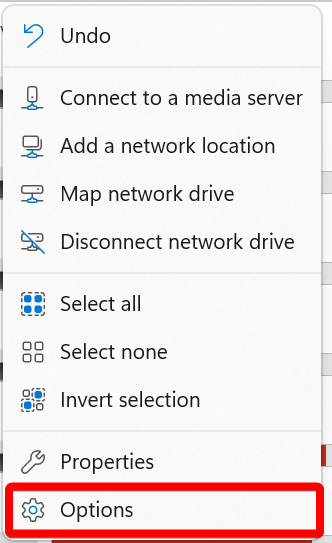
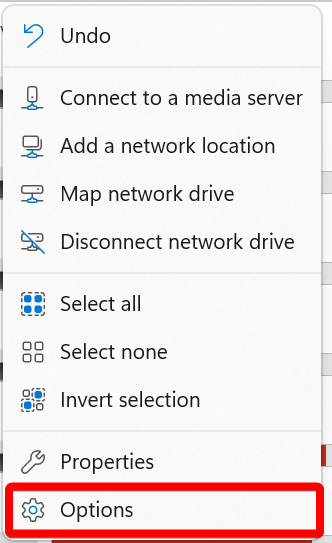
- Now click on the “Options” menu item.
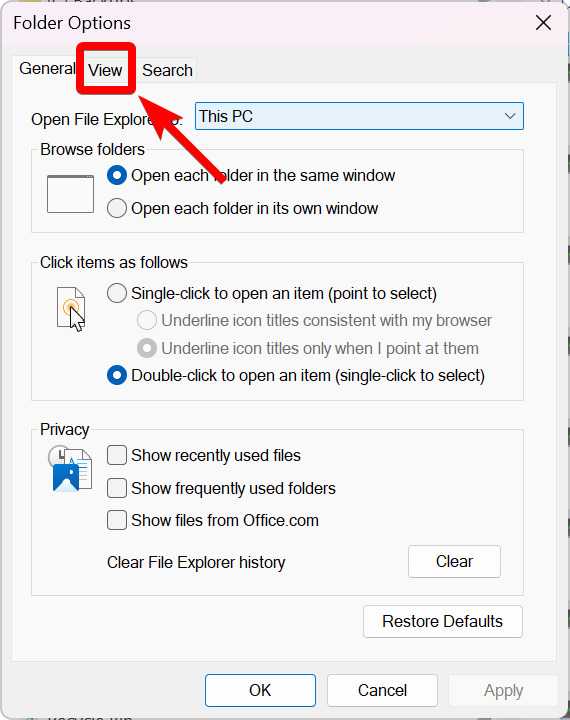
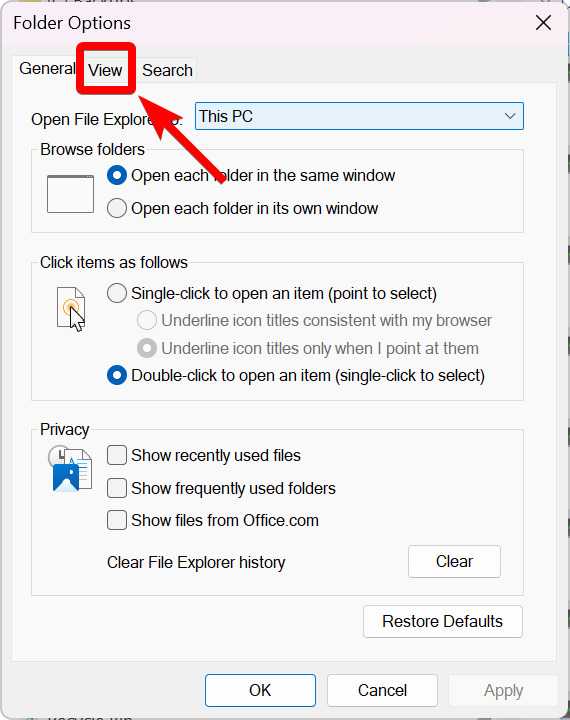
- Click on the “View” tab.
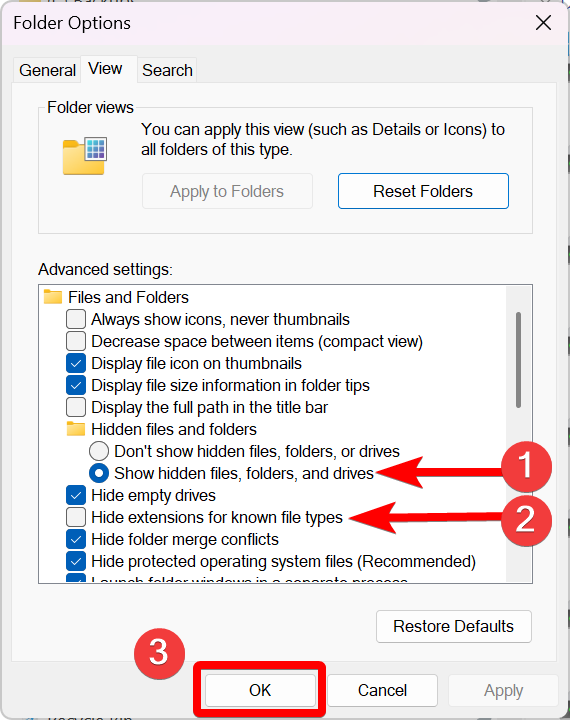
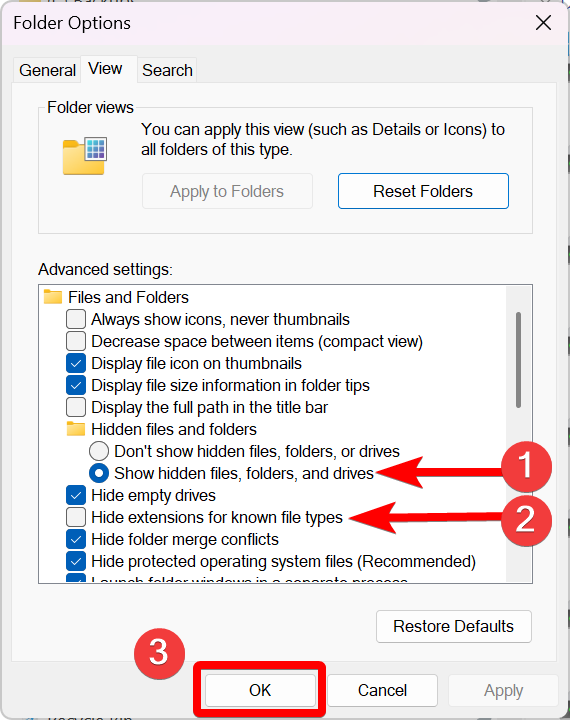
- Now do the following:
- Select the option, “Show hidden files, folders, and drives” (under “Hidden files and folders”).
- Uncheck the option, “Hide extensions for known file types”.
- Click the “OK” button.
That’s it. You now can view file extensions, and view any hidden files and folders on your Windows 11 computer.
I hope you found this tutorial helpful.
Posted in Computers, Internet and Servers, Operating Systems, Tips & Tutorials

Luke 2:8-20 New American Standard Bible (NASB)
8 In the same region there were some shepherds staying out in the fields and keeping watch over their flock by night. 9 And an angel of the Lord suddenly stood before them, and the glory of the Lord shone around them; and they were terribly frightened. 10 But the angel said to them, “Do not be afraid; for behold, I bring you good news of great joy which will be for all the people; 11 for today in the city of David there has been born for you a Savior, who is Christ the Lord. 12 This will be a sign for you: you will find a baby wrapped in cloths and lying in a manger.” 13 And suddenly there appeared with the angel a multitude of the heavenly host praising God and saying,
14 “Glory to God in the highest,
And on earth peace among men with whom He is pleased.”
15 When the angels had gone away from them into heaven, the shepherds began saying to one another, “Let us go straight to Bethlehem then, and see this thing that has happened which the Lord has made known to us.”16 So they came in a hurry and found their way to Mary and Joseph, and the baby as He lay in the manger. 17 When they had seen this, they made known the statement which had been told them about this Child. 18 And all who heard it wondered at the things which were told them by the shepherds. 19 But Mary treasured all these things, pondering them in her heart. 20 The shepherds went back, glorifying and praising God for all that they had heard and seen, just as had been told them.
Posted in Biblical Accounts, Christian, Holiday