How to Enable or Disable Snap Windows in Windows 11
In this short tutorial, I will show you how to enable and disable the Snap Windows feature in Windows 11.
Snap Windows are useful when you want to quickly arrange multiple windows on your desktop. However, they can become irritating and even a hindrance to some people, if you want to position a window on the edge of the screen without triggering auto-snap.
With that little introduction out of the way, let us begin.
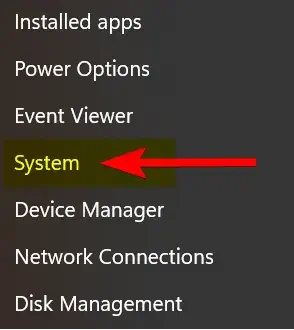
2. On the left-side panel, click on “System”, then click on the “Multitasking” option.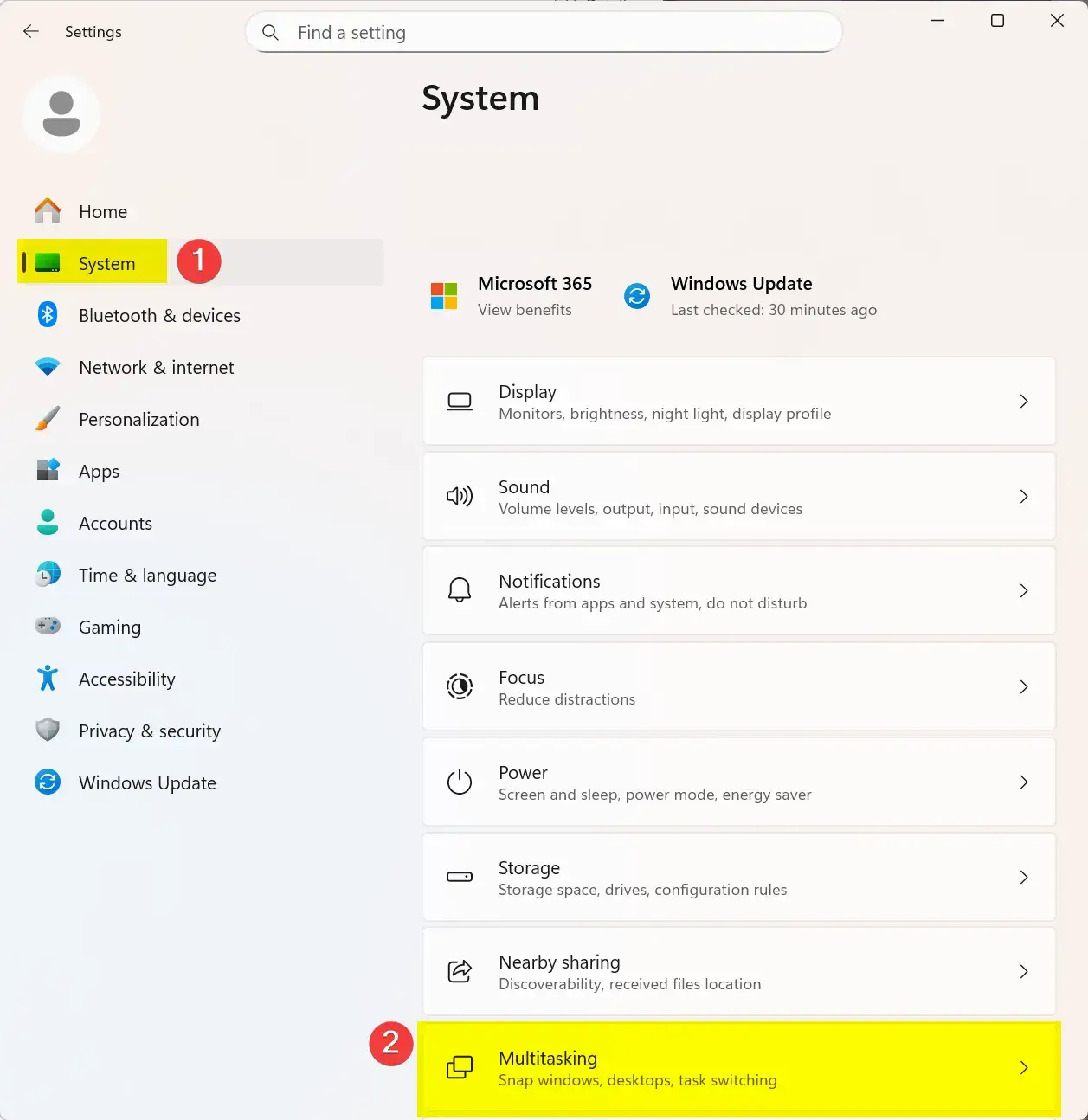
3. Now locate the “Snap windows” option, and click the toggle button to disable it. Of course, if sometime later on you wish to re-enable this feature, just click on the toggle button again to re-enable it.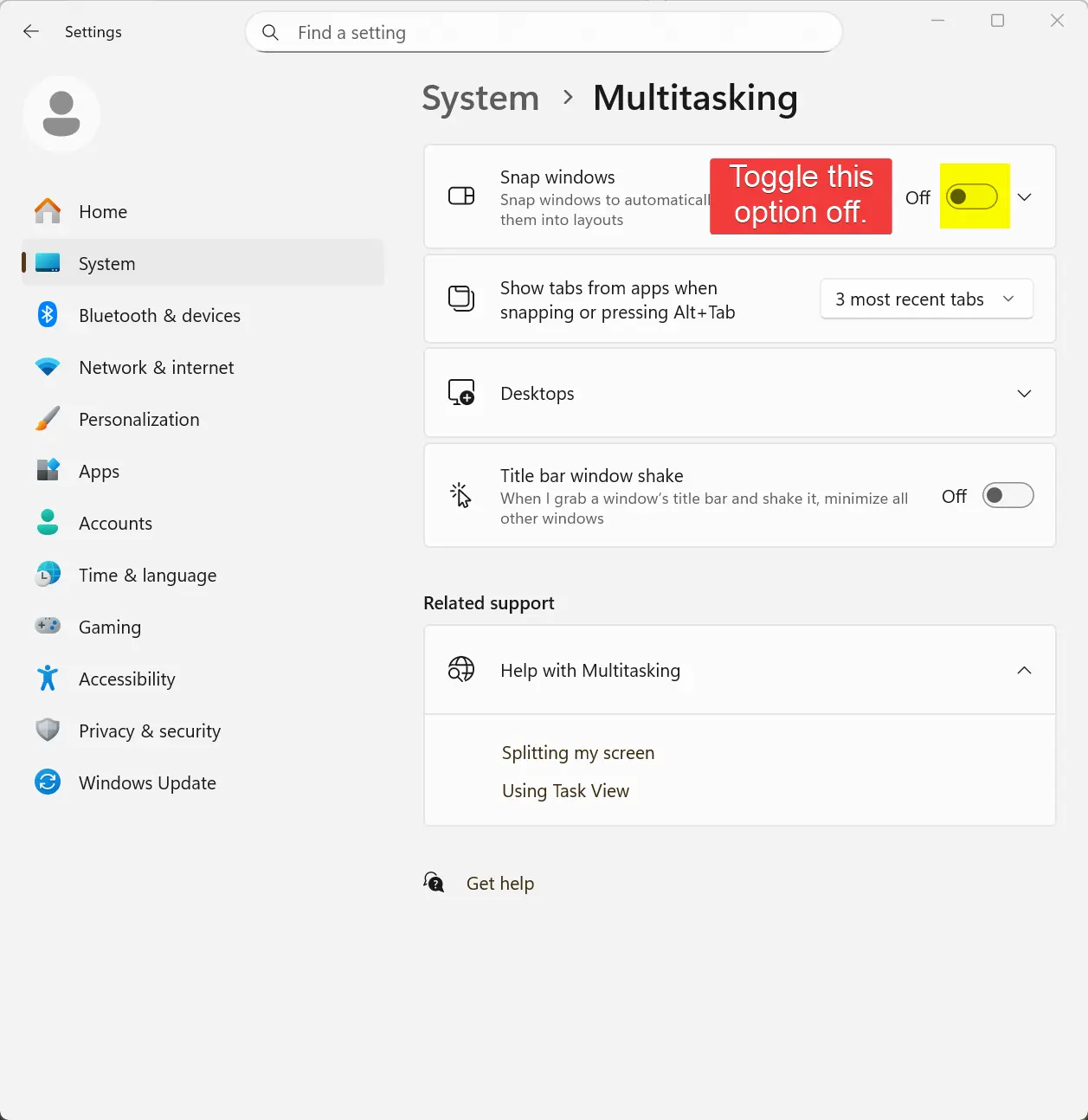
That is the end of this tutorial. I hope someone finds it useful.
Posted in Computers, Operating Systems, Tips & Tutorials
How to Show File Extensions and Hidden Files and Folders on Windows 11
In this blog post, I will explain how to show file extensions, and how to view hidden files and folders on your Windows 11 system.
By default, Windows 11 hides file extensions, and any files and folders marked with the attribute “hidden”. At some point, you may have a need to change a file’s extension manually (e.g., “.txt” to “.ini“). It can also be useful to see any hidden files and folders on your computer.
No reboot is required for these changes to take effect.
- Open the File Explorer.
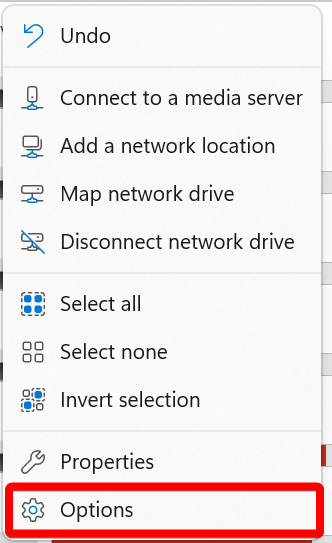
- After the File Explorer opens, click on the ellipsis menu button.
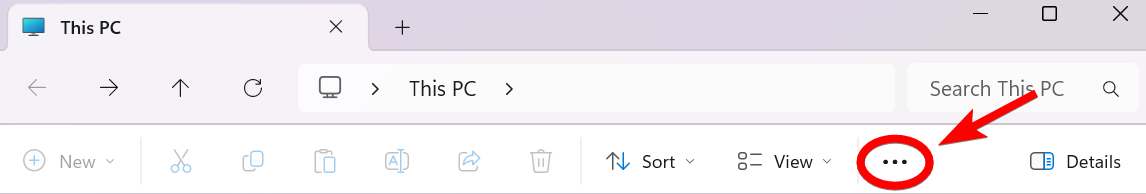
- Now click on the “Options” menu item.
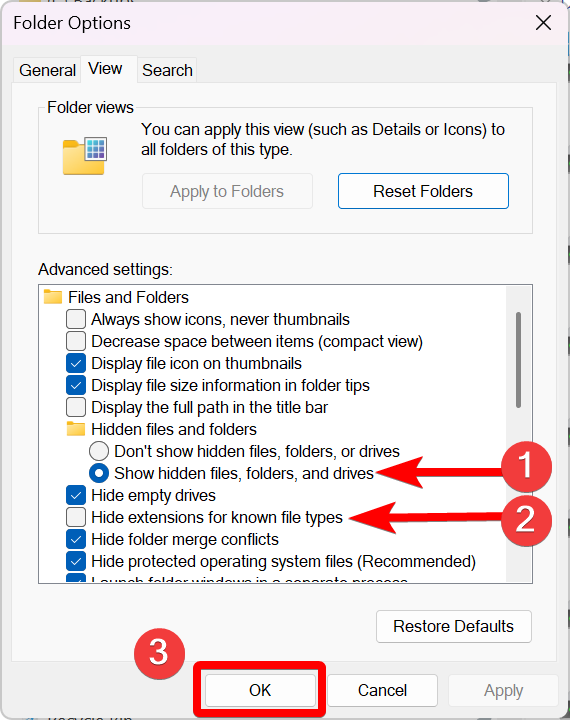
- Click on the “View” tab.
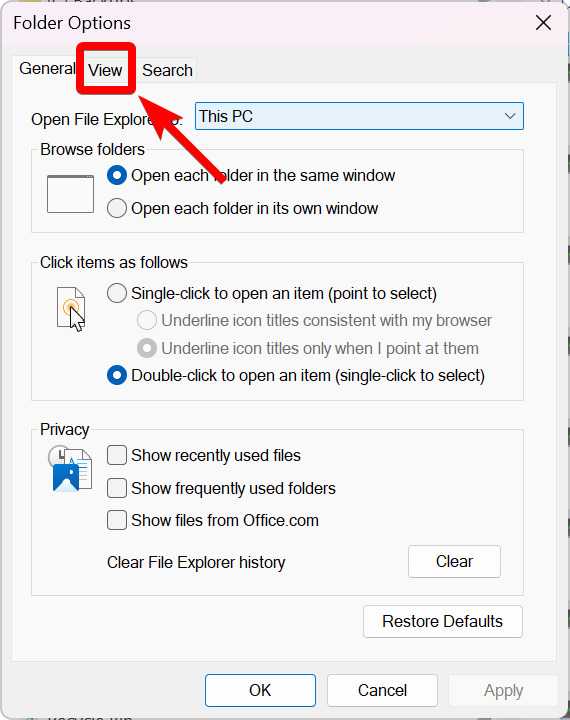
- Now do the following:
That’s it. You now can view file extensions, and view any hidden files and folders on your Windows 11 computer.
I hope you found this tutorial helpful.
Posted in Computers, Internet and Servers, Operating Systems, Tips & Tutorials
How to Reboot Windows using PowerShell for Windows
In this blog post, I will show how to reboot Windows using PowerShell.
As you know, rebooting Windows is typically done through the graphical interface, but understanding how to reboot Windows using PowerShell can be beneficial for various reasons (e.g., automation tasks, install scripts, etc.). Also, you may find yourself in a Windows environment that requires the use of the command line (e.g., Server Core).
You don’t need administrator privileges to reboot a desktop version of Windows, but you do need them to reboot a Windows Server.
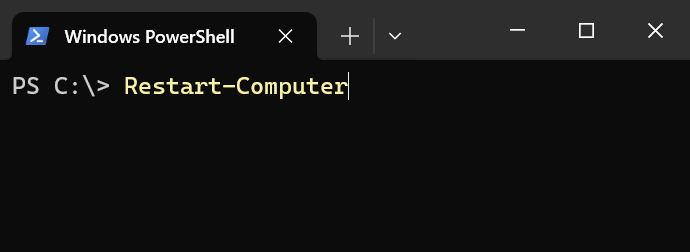
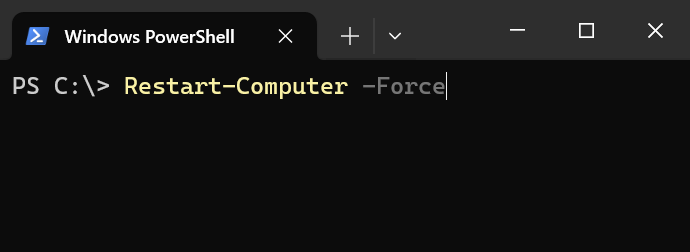
To reboot Windows from the command line, run the following command in a PowerShell terminal.
Restart-ComputerIf you need to forcefully reboot Windows (without waiting for all the programs to close first), use the “-Force” switch.
Restart-Computer -ForcePosted in Code Snippet, Command Prompt, Computers, Internet and Servers, Operating Systems, PowerShell, Tips & Tutorials
How to Disable Windows Memory Compression for Windows 10/11
In this blog post, I will explain how to disable memory compression on a Windows 10/11 system via PowerShell.
For those who don’t know, Windows compresses infrequently used memory instead of writing them to the page file. This way if your computer needs to use that particular data, it just has to decompress it in memory rather than access the much slower page file on your hard drive or SSD.
Since memory compression uses up CPU cycles, this can potentially slow down a computer.
Interesting Fact: Microsoft disables memory compression, by default, on Windows Servers. That right there tells you memory compression can potentially slow down a computer system.
Disabling memory compression on computers with limited RAM ( < 16GB ) can decrease performance rather than improve it. It is always recommended to run benchmarks before and after disabling memory compression to verify that you indeed received a performance increase from turning off memory compression.
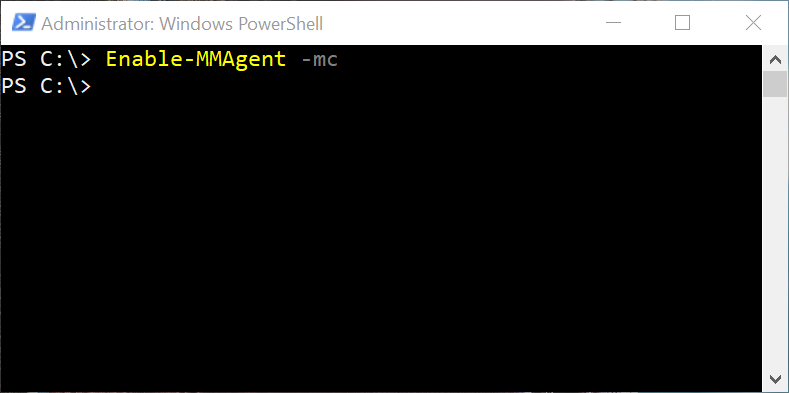
To disable memory compression on Windows 10/11, run the following command in an Administrator PowerShell terminal.
Disable-MMAgent -mc
Of course, if you wish to re-enable memory compression, just type the following command.
Enable-MMAgent -mc
It would probably be a good idea to reboot Windows after disabling or enabling memory compression to make sure the change is applied.
Posted in Code Snippet, Command Prompt, Computers, Internet and Servers, Operating Systems, PowerShell, Tips & Tutorials